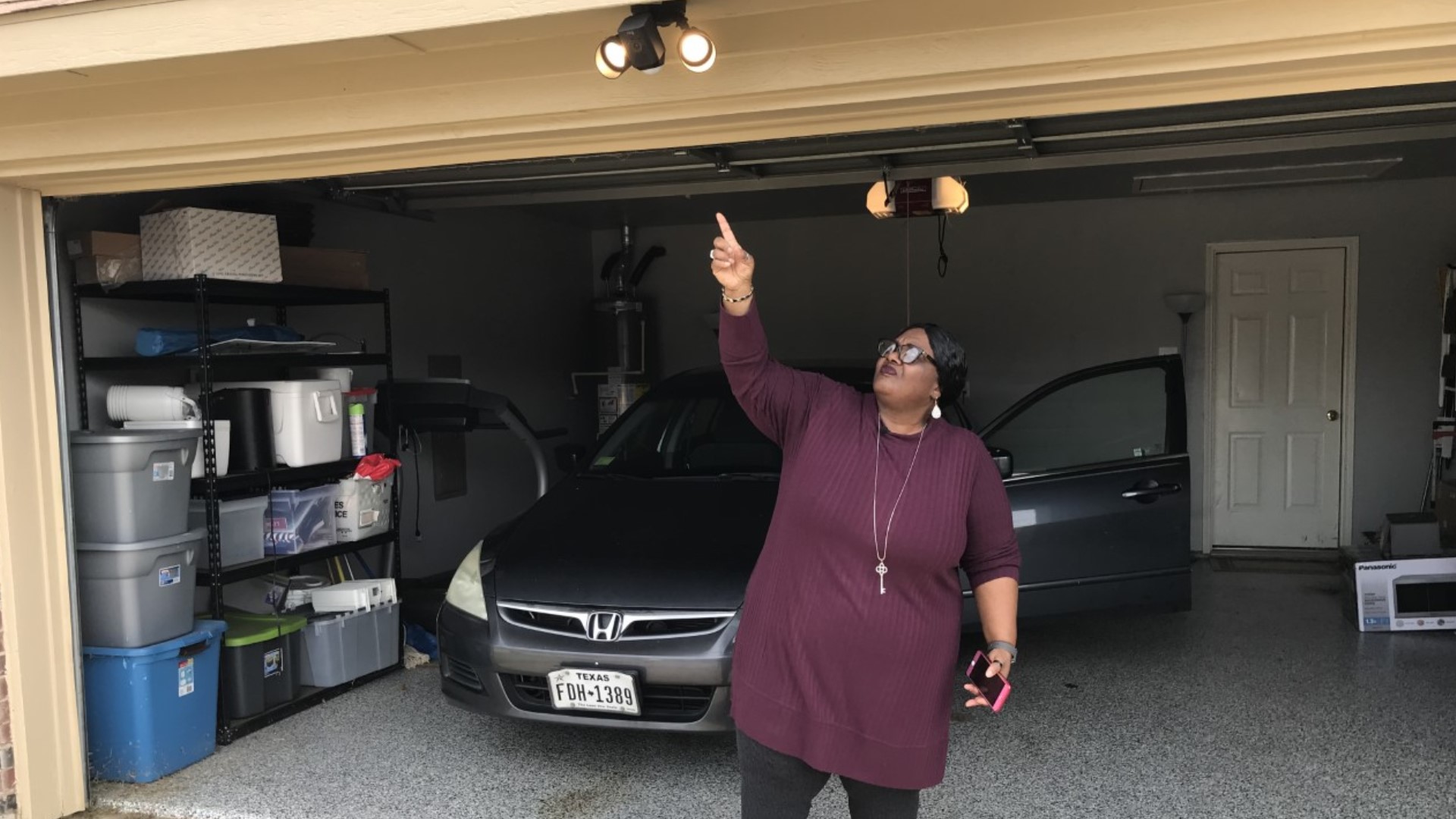
DESOTO, Texas — Sandra Robinson wants to feel safe inside her DeSoto home. To the right of her front door, she has a Ring video doorbell. In the corner of her living room, there is another Ring camera.
She bought a third device for her driveway, but when she tried to set it up, she got this message: "This device is still registered to its owner."
Like most pieces of technology, every Ring camera has a MAC ID, which is like a social security number for technology. For the device to be usable, the owner needs to use that unique number to connect the camera to Wi-Fi.
Robinson is familiar with setting up a Ring camera so she was surprised to see that her newly-purchased device was registered to someone else.
"It's very unsettling," she said.
After contacting Ring, the company told her the camera was connected to someone else but wouldn't say who.
"It makes me think, 'Who in the world is this person?'" Robinson said.
Kelsey, a Ring representative who would not give her full name, said it wouldn't be possible for someone to look through Robinson's camera because of two-step authentication process.


Ring said these types of identification mixups sometimes happen when someone buys a used device, but Robinson bought her camera new from Ring.com. The company couldn't explain how it could happen in this scenario.
Ring told Robinson that the support staff contacted the other person to unregister the device. Only then will Robinson be able to access her camera.
There have been reports of hacked Ring cameras across the country.
In December, Tania Amador told WFAA she heard cryptic messages through her device. Strangers told her to pay a ransom or "get terminated."
Those hacking cases are becoming more common, but cases like Robinson's are more alarming, said Alex Nettles, a lead technician for SpyCentre Security.
Similar to Ring's explanation, Nettles said many cameras that are refurbished or resold might be accidentally still connected to the past user, Nettles said.
He understands how cameras can be hacked but can't figure out how someone else is registered to Robinson's new device.
"That is uncommon," Nettles said. "This is a major issue for this lady."


Unlike Ring, though, Nettles says with the right access and a WiFi connection, someone could see through Robinson's camera.
"She probably does have someone looking through her camera, possibly at this moment," he said.
Ighty Support project manager Kumar Kamalesh said he hasn't heard of this type of problem before with a new product and wouldn't know how to find a solution. Kamalesh has been working on security cameras for a decade.
"It's definitely concerning to this product owner," Kamalesh said.
Ring said Robinson's situation should not be concerning, and it is not a widespread issue.
The Ring representative said the company's two-step authentication process protects users from these types of problems.
"The MAC ID specifically ties the device to the device owner's Ring account and WiFi connection," Kelsey said.
Ring would not reveal who the other person is with the connected MAC ID.
Robinson just wants her device to work.
"I'm also paying for, being able to view the camera, so why not give me a camera that I'm able to install successfully and able to view on my network?" Robinson said.